If you know anything about computers, you know that every single one needs an operating system. A computer without an operating system is little more than an expensive paperweight. The number of operating systems in the world is high, with the most common being the Microsoft Corporation’s Windows operating system and Apple’s iOS. However, a lesser-known but equally effective operating system is the open-source Linux operating system.
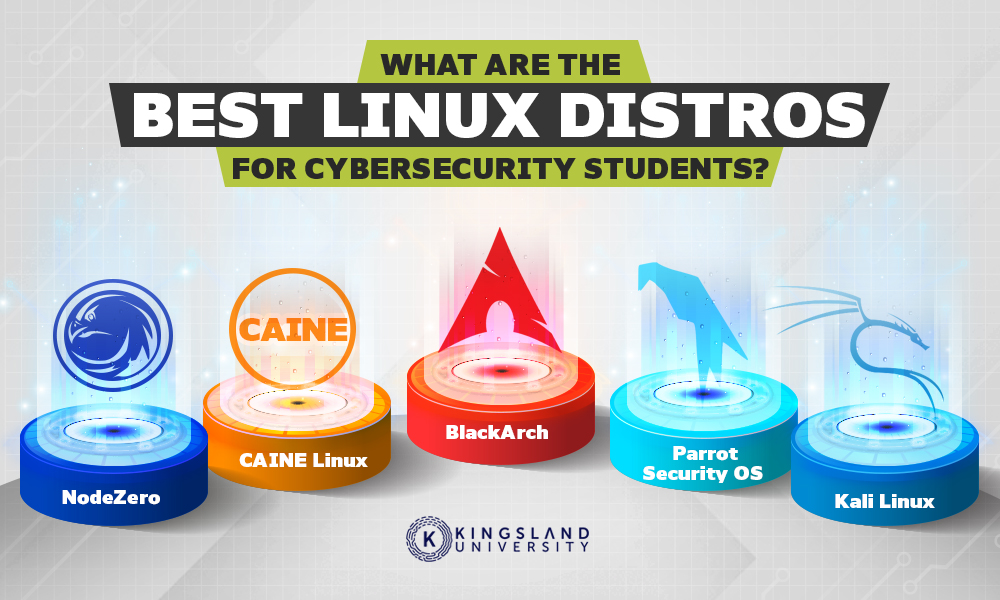
While the use of Linux is not as widespread as the others, it still has a place in modern technology. For example, it’s a powerful platform for digital security. The real question is which version of Linux is best suited for you if you are aspiring to be a cybersecurity professional.
What is Cybersecurity?
If you are looking into becoming a professional in cybersecurity, it might benefit you to understand what is expected of you fully. Cybersecurity is the protection of devices and their associated data from coming into the possession of unauthorized individuals. Almost everything we do is online now due to convenience and efficiency. We shop online, we communicate online, and we store personal information and images online. This means that our credit cards, location, and personal information can all be accessed by strangers if they are not adequately protected.

To defend against these attempts to acquire our personal information, virtually every personal device on the planet has a security program installed. Favored anti-virus software like Kaspersky or Norton is used to protect against hostile programs or hacking attempts from trojan horse programs that piggyback on otherwise legitimate downloads. This software has become such a critical component of our computer use that those who would exploit weaknesses in the system for their own gain have to constantly update and enhance their methods to get ahead of what protects us.
Cybersecurity professionals are the ones who not only create the software we use to protect our information but they also maintain it. When hackers develop new tactics for circumventing antiviral software or cybersecurity programs, professionals analyze the tactics and update the programs to defend against the new tactic. They even find themselves engaging in counter-hacking attempts when the stolen information is sensitive enough to warrant further investigation. Every major law enforcement agency in the world now has a cybernetic crimes division that employs cybersecurity professionals to conduct these investigations and follow the digital trail back to these hostile hackers.
What is Linux?
Linux is a collection of open-source, modular operating systems with a vast array of versions and distributions. The Linux family of operating systems is UNIX-like, meaning that they function similarly to the UNIX operating system, which was capable of advanced multitasking.
The original distribution of the Linux software was released on September 27th in 1991. It was targeted as software that could power personal devices with the added benefit of serving as an open-source option, making it free for all, amid more prominent and expensive options like the early builds of Windows and Apple’s OS. Linux was built on the Intel x86 software architecture concept and remains the most prominent example of general-purpose software. Contemporarily, Linux can be found on computers, mobile devices, and smart devices like televisions.
While Linux is only used by about 2.3% of all desktop computer users, it remains a viable option for specific tasks, including cybersecurity. In fact, there are even specific Linux distros that are engineered as cybersecurity platforms. Some of those are included below.
Distro #1: Kali Linux
Released on March 13th, 2013, the Kali Linux, formerly known as BackTrack, distribution of the Linux operating system was developed by Offensive Security and is derived from the Debian distribution of Linux. Unlike other variations of the Linux operating system, Kali Linux’s developer is a world-class provider of information security and penetration training. In addition to providing an ideal operating system for use by cybersecurity personnel, Offensive Security helps train the professionals.

When BackTrack was initially released, it was based on the Knoppix distribution of Linux and focused on security. When Kali Linux went up, it was with a whole new suite of tools and code. The main tools found with Kali Linux are:
- Burp Suite: A tool for web application penetration testing.
- Wireshark: A network protocol analysis tool.
- Aircrack-ng: A wireless cracking tool.
- Hydra: A tool for online brute force password hacking.
- Maltego: A tool for intelligence gathering.
- John: An offline equivalent for Hydra’s password cracking.
- Metasploit Framework: A tool to exploit security weaknesses.
- Owasp-zap: A tool to find vulnerabilities in applications.
- Nmap: A network scanner.
- Sqlmap: A tool to exploit vulnerabilities in SQL injections.
With the tools available to Kali Linux’s suite and the original role of the developers, Kali Linux is a strong contender for cybersecurity professionals. However, it is only one of many Linux distributions available for the industry. Kali Linux is not only one of the top-rated distributions of Linux but also one of the more recommended for students.
“This is a great OS. I love that it comes preloaded with a lot of the necessary tools and can be bootable from just a flash drive. It is so lightweight and a great utility. I have used it pretty extensively in school in labs for a “CTF” competition and various other projects. I have also used it professionally to test some of our security measures.
What are the pros?
+Lightweight
+Bootable from flash drive (no install)
+All the tools and utilities loaded with it
What are the cons?
-None come to mind” –Stay_Dandy, SpiceWorks.
Distro #2: NodeZero
While the information on who made the NodeZero distribution of Linux is unavailable, it is known that the operating system was originally released on October 6th, 2010. NodeZero was built around the Ubuntu distribution of the original Linux software as a complete system designed with penetration testing in mind. Penetration testing, or ethical hacking, is a key responsibility for those in the cybersecurity industry.

NodeZero comes with over three hundred tools for penetration testing and security. It also comes with the THC IPV6 Attack Toolkit, which features tools such as live6, dnsdict6, and toobig6 for penetration and security testing. Unlike Kali Linux, NodeZero is more of a source code style, making it more difficult to work with if you are not an established user of Linux software.
Distro #3: Parrot Security OS
Another Debian-based Linux distribution, Parrot Security (ParrotSec) is a Linux distribution released on the 10th of April in 2013. Parrot Security was created by Lorenzo “Palinuro” Faletra and the Frozenbox team with the goal of creating an operating system for penetration testing, vulnerability assessment and mitigation, computer forensics, and anonymous browsing.
Unlike other Linux operating systems, ParrotSec combines features from Frozenbox (Another Linux distribution) and Kali Linux to create a new operating system. One benefit that Parrot Security OS has over Kali Linux is the anonymity tools. ParrotSec allows the user to completely hide their identities when surfing the Internet and therefore remain relatively undetectable when engaging in cybersecurity counterattacks against hack attempts. Like Kali Linux, Parrot Security is one of the Linux distributions recommended for students.
“I like that it has already all the security software pre-installed and that it is configured to start safely. You pretty much don’t have to set up anything.
It is definitely not user-friendly for those who don’t already know how to use Linux. Also, it is extremely safe which implies that some convenience features are not working.
Know your Linux skills first
A safe system with ok performances. I was using Zorin before which is very convenient but a bit less safe.” –Anonymous, G2.
“Parrot is the latest distribution of Linux releases it has integrated security assessment tools for security professionals it has Metasploit, Burpsuite, SQLmap and so many penetration testing tools that were integrated into the operating system. all tools are integrated into one operating system and no need to install one by one.
Most of the Parrot-OS security tools are based on the command line if they can introduce inbuilt GUI-based security tools it will be great.
We are using parrot security OS it has more features than Kali Linux there are more inbuilt exploitation libraries.
We are using ParrotOS to perform penetration testings to our clients.” – Anonymous, G2.
Distro #4: BlackArch
Another penetration-testing-oriented distribution of the Linux operating software, BlackArch is functionally like the previously mentioned Parrot Security and Kali Linux distributions. Unlike the others, however, BlackArch does not offer desktop functionality. Instead, the operating system opts for preconfigured windows in which to process commands. Developed by a small group of cybersecurity specialists, the BlackArch software offers over two thousand tools dedicated to penetration testing.
BlackArch is one of the better interfaces for devices that will only serve a purpose for cybersecurity tools. While BlackArch is recommended for students, some reviews have posited that it is more complicated than one might expect.
“The Net Installer allows you to build your installation from scratch. This allows you to limit the extra software required and run a lean, mean, pentest machine. I appreciate the responsiveness and lack of overhead resource usage. The ability to ignore the GUI and operate 100% CLI is excellent.
There is currently nothing in the distro that I dislike. It is complete and straightforward, though not for the uninitiated.
Ensure you are very familiar with Linux and its various nuances. Though a GUI is available, knowledge of the CLI is a must to use this distro to the fullest.
Internal and external penetration and security testing for our corporate and satellite offices.” – Anonymous, G2.
Distro #5: CAINE Linux
An Ubuntu-based variation of the Linux software, the Computer-Aided Investigative Environment (CAINE) began development under Giovanni Bassetti in 2008. CAINE was created as part of a project for digital forensics software, organizing cyber forensic tools with a user-friendly graphical interface. CAINE offers several tools to aid in the forensic analysis needed for cybersecurity professionals:
- The Sleuth Kit: A tool for inputting open-source command lines to execute commands to analyze file systems and disk volume.
- Autopsy: Serving as the graphical interface for the Sleuth Kit, the Autopsy tool is designed to execute forensic analysis of files and search for specific keywords and web artifacts.
- RegRipper: A tool that extracts and parses information from files stored in a device.
- Tinfoleak: A tool dedicated to the analysis of Twitter posts and accounts.
- Wireshark: This tool collates network traffic, and analyses data packet captures.
- PhotoRec: An especially useful tool that facilitates the recovery of deleted files and documents directly from the hard drive.
- Fsstat: This tool displays the statistical data for images and storage devices.

As a forensics tool, CAINE is the sort of operating system that would likely see more use among cybersecurity professionals employed by law enforcement agencies. Its toolset is dedicated to extracting incriminating information stored on a suspect’s personal device. However, the tool can also be useful for those seeking to understand how information is retrieved to develop countermeasures to protect privacy. While CAINE is more likely to be used by professionals, its user-friendly graphical interface makes it worthy of consideration for even students looking into this niche sect of cybersecurity.
The Final Choice
Cybersecurity is an emerging field with almost limitless potential for growth and expansion but requires the right tools to really get involved. If you are interested in joining the ranks of a professional cybersecurity firm and are partial to Linux operating systems, any of these distributions should be more than helpful in keeping you up to snuff.
Each distribution of the Linux operating software was developed by individuals who want to custom tailor it to what they feel is the best version for cybersecurity purposes. Each one will have different advantages and shortcomings. If you are unsure about which Linux distribution will best suit you, the best detail is that you can try them all out without a penalty since they are all open-source and will not cost you a dime. However, if reviews are any indication, Kali Linux appears to be the top contender.
Ultimately, which distribution appeals to you is your decision. If any of these distributions, or any that were not listed here, appeals to you, take the plunge and see how well it meshes with your current aptitude for cybersecurity tasks.

