
Cybersecurity is a continuously growing field. More and more of the world’s business, commerce, information processing, data storage, and personal information is handled online. Entire businesses exist solely because of cloud-based applications, and the days of the on-premises network are swiftly fading.
Because of this, cyber-crime is a growing industry. There are decades worth of viruses and exploits circulating online, waiting to pounce on the right vulnerable surface given a chance. There are thousands of individuals and organizations working to compromise systems.
Think of all the threats out there.
- Individual hackers testing their skill against secured systems, either bug hunting for personal gain or simply hoping to cause some destruction.
- Script kiddies running scripts given to them by more organized groups meant to compromise systems or DDoS platforms and let more sophisticated attackers get in.
- Hacking groups developing and spreading malware that exploits transmission protocols or zero-day bugs to ransom entire systems. See Heartbleed as an example.
- Organized crime groups like the mafia adapting to new forms of crimes they can exploit.
- Terrorist organizations realizing that a single well-placed cyber-attack can do more damage from a safer position than nearly any bomb could.
- Nation-state actors taking traditional ideas of warfare off the street and away from the seas in favor of more insidious and potentially damaging cyber-attacks.
Whether you intend to protect a company against all of China or Iran, or against Dave’s nephew looking to see what he can do, cybersecurity is a growing field with openings in virtually every industry. Anything that uses networked technology is vulnerable to cyber-attacks, and that means cybersecurity experts are in demand.
What industries are in the greatest need? The answer tends to change from year to year. As it stands today, at the end of 2020 and moving into 2021, a few industries stand out above the rest.
Healthcare
The healthcare industry around the world has been put under more stress this year than it has in decades. A pandemic with questionable handling already puts a lot of stress on the healthcare system. This is in the midst of a global push to transition from paper records to Electronic Healthcare Records systems.
EHRs aren’t just any computer system, either. They need to be a secure internal network, to manage an individual facility and its records. They need to be networked, to communicate with other facilities in the same network, such as linked hospitals and hospital-adjacent facilities. They need to be accessible and available to transmit information to other EHR systems when a patient moves to another location or their records are needed in an out-of-network facility, potentially even in other countries, not just cities or states.
On top of this, healthcare systems manage incredible amounts of data. They have to manage financial and billing information, and all of the information working with insurance entails. They have to manage patient records. They have to manage medication records, prescription control, and all of the regulations involved with controlled substances, stopping abuse, and even theft from employees. And all of this, the whole time, is subject to strict industry regulations, including HIPAA.

The global pandemic has only shed more light on this. On the one hand, nations and authorities around the world are appealing to the better nature of criminals to stop healthcare attacks, in the same way, that medics are meant to be protected even on a battlefield. On the other hand, healthcare facilities make juicy targets for ransomware and other cybercrime, and that has only ramped up throughout the pandemic as the systems become more and more vital, and more and more vulnerable.
Healthcare cybersecurity faces a large challenge of getting already-overworked doctors, nurses, and other staff to practice proper cybersecurity habits. Anyone choosing to specialize in healthcare cybersecurity has their work cut out for them and needs to have a deep understanding of security practices that enforce employee habits, as well as technical security and network security. It’s an intense job, but it’s also one of the few areas where cybersecurity may save someone’s life, rather than just their money or their assets.
Manufacturing
Factories and facilities have a bad reputation among IT workers, largely because they tend to operate on out-of-date technologies. It’s not uncommon to need to debug a program running on an ancient installation of Windows 2000 or earlier, because the vendor that made the control software for some million-dollar factory machine hasn’t existed since 2005 and the software has been long abandoned. This happens around the world and is a very difficult problem to solve.
Modern upgrades to manufacturing facilities bring with them modern technology. These technologies, dubbed Industry 4.0, make heavy use of networked appliances and the Internet of Things. If you’re sufficiently knowledgeable about cybersecurity, this likely made you shudder at the thought.

The Internet of Things is an interesting blend of networked devices and functionality, but IoT products are notorious for their issues, ranging from well-known security vulnerabilities to a lack of support to the companies who originally made them disappearing. Anyone looking to go into manufacturing security will need to confront these issues and the friction between the inherent flaws in IoT devices and the need to update extremely old and vulnerable machines for a modern age before something breaks.
Manufacturing as an industry also has associated industries with their own cybersecurity issues and unique threat vectors. Manufacturing is where some of the most cutting-edge non-military robot applications are coming into play, and customized software for robots needs customized security. Asset tracking can also be a large threat surface similar to medication tracking in healthcare.
Manufacturing has done a lot to modernize over the last decade, and one modernization practice is involving smartphones in a lot of business processes. This becomes a large threat vector as well, as mobile devices can be compromised easily and can become an entry point for malware. In manufacturing, ransomware is quite a common threat, as is phishing.
Finance
It should come as no surprise that the financial sector is one of the most targeted industries in the world, for both traditional crime and cyber-crime. Insights from 2019 indicate that the financial industry is the target of nearly a quarter of all cyber-attacks around the world.
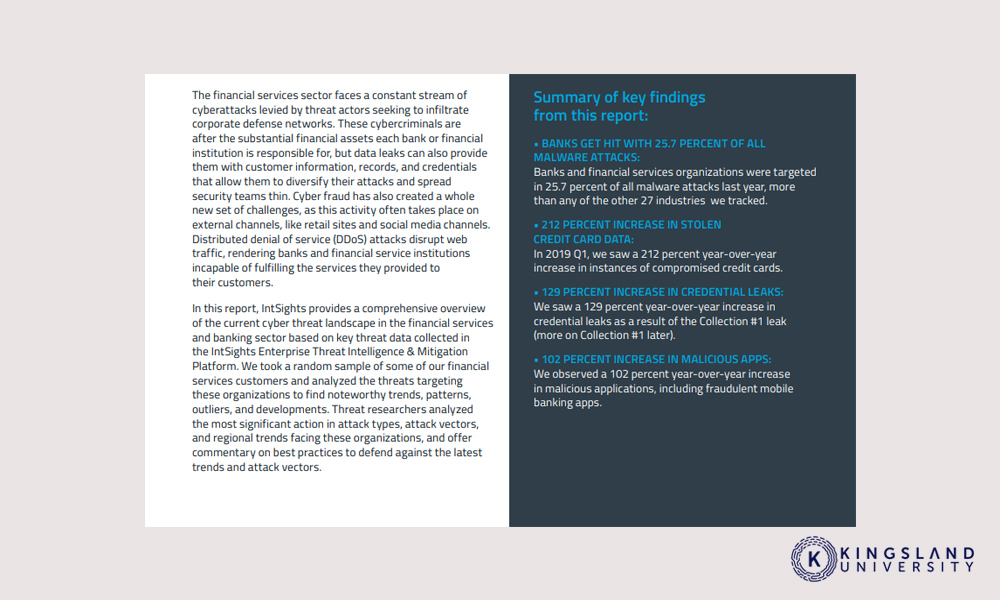
Finance applies in a wide range of possible institutions. Major banks are one of the most obvious, and while they are well-versed in hiring cybersecurity experts, they’re always in need of more. Smaller banks and credit unions also need protection, and usually have fewer resources to go about it.
Financial services need their own forms of protection. Everything from investment firms to financial planners to the financial services and payment processors who handle financial transactions for retail outlets and online stores is all vulnerable. Whether it’s Square, PayPal, Google-Pay, Amazon, or just your local mom and pop retail outlet, some manner of financial protection needs to be in place. Keeping in mind as well that personal information and financial information is heavily regulated and must be protected above and beyond traditional business security policies.
Financial institutions are similar to healthcare facilities in that they often have large numbers of employees accessing sensitive systems without an adequate understanding of cybersecurity, the practices involved, and the needs of the company in securing systems and data. Network-level security is critical, as is training, as is implementing policies that make sense and are less cumbersome than the alternatives while still providing adequate security.
Some of the most sophisticated cyber-threats in the world are aimed at financial institutions. Detecting signs of those intrusions, and protecting against them, is a cutting-edge field. Anyone looking to pursue a career in cybersecurity with a focus on the new and most innovative threat-and-response scenarios will do well in a financial security role.
Retail
What do the companies Equifax, Adobe, eBay, Marriott, Target, and Home Depot have in common? They are all companies that have experienced massive data breaches and exposed millions of people’s personal information.
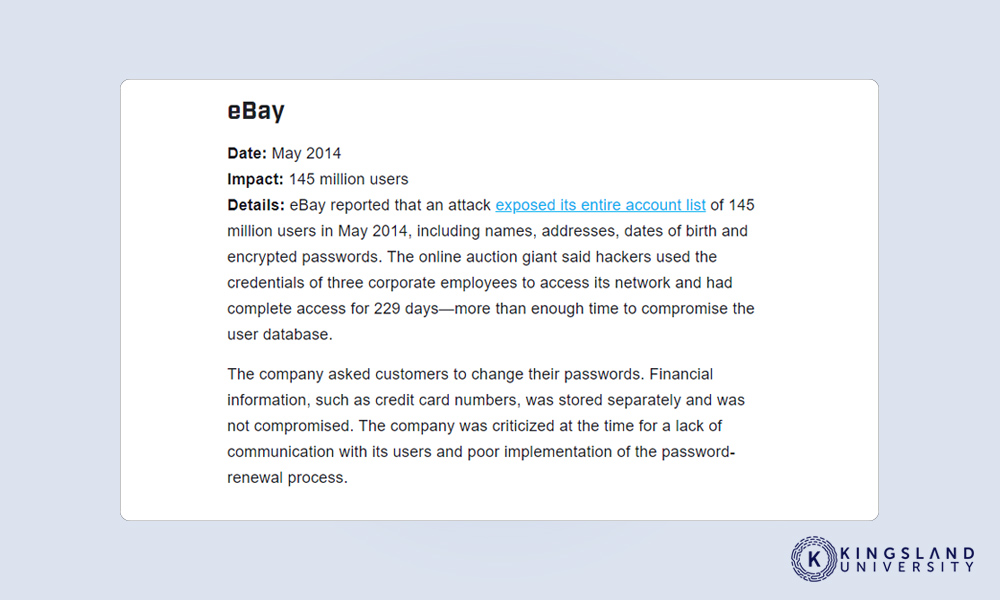
The retail industry is tied in with the financial industry because they process billions of payments every day. They’re an incredible vector for a cyber-attack, due to the lack of standards and regulation across the industry and the wide variety of different scenarios and technologies used across the board. Every retail company, it seems, is different in how they handle their security, and very few of them seem to have gotten it right.
Some major retailers, like Amazon, are going to be at the cutting edge of cybersecurity by necessity. Amazon itself has its retail arm, but they also have the Amazon Web Services system and all of the security that entails. Smaller companies have just as much need for a secure network and infrastructure, however, and an expert who can come in, audit, improve, and secure a facility can be a great asset for a huge array of companies around the world.
Retail will forever be in need of talented cybersecurity employees, from the ground-level workers who train other employees in proper practices to the network architects and security directors who are responsible for securing entire systems from the top down.
Government
While it can often seem like many areas of the government are perpetually decades behind the times in terms of practices, security is something they rarely ignore. At the federal level, the government is a massive employer of cybersecurity experts, because it is a massive target for some of the most sophisticated and high-level attacks out there. Cybersecurity training from the ground up is essential.
Security regulations are tight and ever-changing to meet the changing times. Technology must be strictly regulated and audited, and the higher level the position, the stricter it gets. Some of the most brilliant cybersecurity minds are employed by the government, both on defense and on offense.
If you want to pursue a career in cybersecurity with an aim to work for the government, you may also desire to earn a security clearance and pursue various opportunities such as security internships in D.C. and some of the specific kinds of training available from the National Initiative for Cybersecurity Careers and Studies.
Utilities
One often under-represented industry at risk from cyber-attack is utility companies. Whether it’s water companies, power companies, the control software for dams, or the national power grid, a ton of modern technology goes into regulating, tracking, and manipulating utilities for hundreds of millions of people.
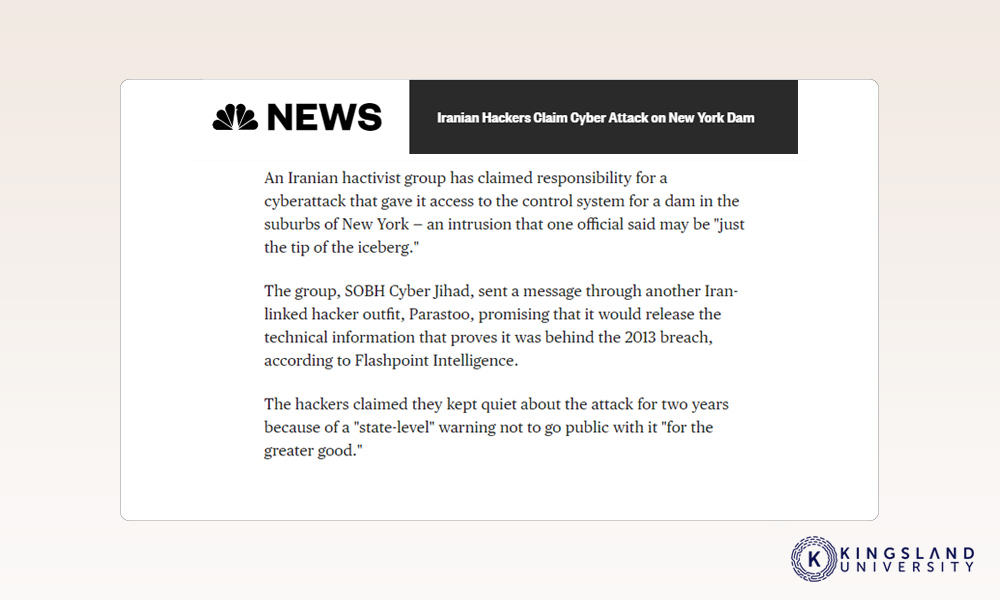
Energy companies in particular are both highly regulated and subject to compliance laws and audits. This is great for certain kinds of restrictions, including physical security, but can often be a detriment to the adoption of new security technologies. Securing utilities is a matter of life and death for many people, and can cripple or destroy industries if poorly regulated.
Maintaining proper security for utilities is often a matter of awareness and recognition of the threats these usually-invisible providers face. With broadly distributed facilities that nevertheless require networking, digital security is more important than ever.
Broadening Demand
All of this is not to say that other industries are safer, or less targeted. The reality is that many attackers are attackers of opportunity. They don’t pick a business and try to hack it, they pick an underlying system or exploit and look for organizations using that system without security in place.
Pretty much every industry around the world has a need for cybersecurity in the modern era. Our increasing reliance on computers and networking to do work for us and handle communications means that security threats are going to continue to grow in seriousness for the indefinite future. As long as there are networks to exploit, there will be attackers looking to exploit them.

Bear in mind that most cybersecurity training is sufficient to prepare you for the entry-level positions and certifications necessary to begin a security career. Specializing can come later when you determine the kind of security you would be interested in pursuing, what industry you would want to protect, and how you would want to grow your career. Needless to say, there will be openings available indefinitely.

